Xp Patch W32 Blaster Virus Software
Blaster worm spreading; experts warn. Referred to alternately as W32.Blaster. Security experts also recommend installing firewall and antivirus software to.
Of the Blaster worm, showing a message left for founder by the programmer Blaster Worm (also known as Lovsan, Lovesan or MSBlast) is a that spread on computers running and, during August 2003. The worm was first noticed and started spreading on August 11, 2003. The rate that it spread increased until the number of infections peaked on August 13, 2003. Once a network (such as a company or university) was infected, it spread quicker within the network because firewalls typically did not prevent internal machines from using a certain port.
Filtering by ISPs and widespread publicity about the worm curbed the spread of Blaster. On March 12, 2004, Jeffrey Lee Parson, an 18-year-old from, was arrested for creating the B variant of the Blaster worm; he admitted responsibility and was sentenced to an 18-month prison term in January 2005. Contents. Creation and effects According to court papers, the original Blaster was created after security researchers from the Chinese group Xfocus reverse engineered the original Microsoft patch that allowed for execution of the attack. The worm spreads by exploiting a discovered by the Polish security research group Last Stage of Delirium in the service on the affected operating systems, for which a patch had been released one month earlier in and later in. This allowed the worm to spread without users opening attachments simply by spamming itself to large numbers of random IP addresses.
Four versions have been detected in the wild. These are the most well known exploits of the original flaw in RPC, but there were in fact another 12 different vulnerabilities which never saw very much media attention. The worm was programmed to start a against port 80 of if the system date is after August 15 and before December 31st and after the 15th day of other months, thereby creating a (DDoS) against the site. The damage to Microsoft was minimal as the site targeted was windowsupdate.com, rather than windowsupdate.microsoft.com to which the former was redirected. Microsoft temporarily shut down the targeted site to minimize potential effects from the worm. The worm's executable, MSBlast.exe, contains two messages. The first reads: I just want to say LOVE YOU SAN!!
This message gave the worm the alternative name of Lovesan. The second reads: billy gates why do you make this possible? Stop making money and fix your software!! This is a message to, the of Microsoft and the target of the worm. The worm also creates the following registry entry so that it is launched every time Windows starts: HKEYLOCALMACHINE SOFTWARE Microsoft Windows CurrentVersion Run windows auto update=msblast.exe Timeline.
May 28, 2003: Microsoft releases a patch that would protect users from an exploit in WebDAV that Welchia used. (Welchia used the same exploit as MSBlast but had an additional method of propagation that was fixed in this patch. This method was only used after 200,000 RPC DCOM attacks - the form that MSBlast used).
W32 Virus Warning
July 5, 2003: Timestamp for the patch that Microsoft releases on the 16th. July 16, 2003: Microsoft releases a patch that would protect users from the yet unknown MSBlast. At the same time they also released a bulletin describing the exploit. Around July 16, 2003: White hat hackers create proof-of-concept code verifying that the unpatched systems are vulnerable. The code was not released. July 17, 2003: CERT/CC releases a warning and suggests blocking port 135.
July 21, 2003: CERT/CC suggests also blocking ports 139 and 445. July 25, 2003: xFocus releases information on how to exploit the RPC bug that Microsoft released the July 16 patch to fix. August 1, 2003: The U.S. Issues an alert to be on the lookout for malware exploiting the RPC bug. Sometime prior to August 11, 2003: Other viruses using the RPC exploit exist.
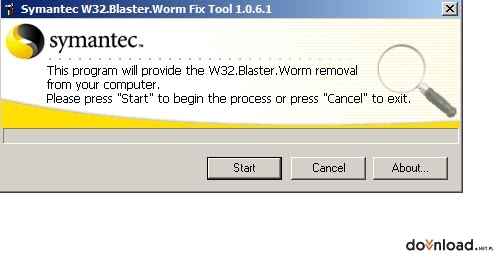
August 11, 2003: Original version of the worm appears on the Internet. August 11, 2003: Symantec Antivirus releases a rapid release protection update. August 11, 2003, evening: antivirus and security firms issued alerts to run Windows Update. August 12, 2003: The number of infected systems is reported at 30,000. August 13, 2003: Two new worms appear and begin to spread. (Sophos, a variant of MSBlast and W32/RpcSpybot-A, a totally new worm that used the same exploit). August 15, 2003:The number of infected systems is reported at 423,000.
August 16, 2003: DDoS attack against windowsupdate.com starts. (Largely unsuccessful because that url is merely a redirect to the real site, windowsupdate.microsoft.com). August 18, 2003: Microsoft issues an alert regarding MSBlast and its variants. August 18, 2003: The related, appears on the internet.
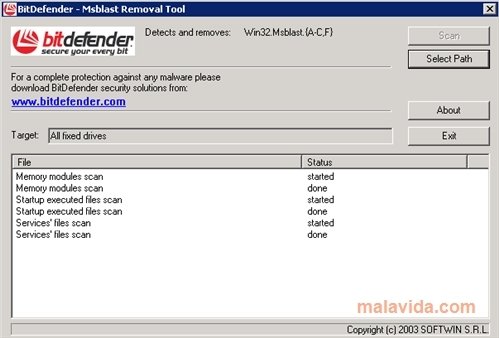
August 19, 2003: Symantec upgrades their risk assessment of Welchia to 'high' (category 4). August 25, 2003: McAfee lowers their risk assessment to 'Medium'. August 27, 2003: A potential DDoS attack against HP is discovered in one variant of the worm. January 1, 2004: Welchia deletes itself. January 13, 2004: Microsoft releases a stand-alone tool to remove the MSBlast worm and its variants. February 15, 2004: A variant of the related worm Welchia is discovered on the internet. February 26, 2004: Symantec lowers their risk assessment 'Low' (category 2).
(Actually this pertains to the related worm Welchia, not to MSBlast itself). March 12, 2004: McAfee lowers their risk assessment to 'Low'. April 21, 2004: Another variant is discovered.
January 28, 2005: The creator of the 'B' variant of MSBlaster is sentenced to 18 months in prison. Side effects Although the worm can only spread on systems running Windows 2000 or Windows XP (32 bit) it can cause instability in the RPC service on systems running, and. In particular, the worm does not spread in Windows Server 2003 because Windows Server 2003 was compiled with the /GS switch, which detected the buffer overflow and shut the RPCSS process down. When infection occurs, the buffer overflow causes the RPC service to crash, leading Windows to display the following message and then automatically reboot, usually after 60 seconds. “ System Shutdown: This system is shutting down. Please save all work in progress and log off.
Any unsaved changes will be lost. This shutdown was initiated by NT AUTHORITY SYSTEM Time before shutdown: hours:minutes:seconds Message: Windows must now restart because the Remote Procedure Call (RPC) Service terminated unexpectedly. ” This was the first indication many users had an infection; it often occurred a few minutes after every startup on compromised machines. A simple resolution to stop countdown is to run the 'shutdown /a' command in the Windows command line, causing some side effects such as an empty (without users) Welcome Screen. The worm had a similar effect.
Months later, the surfaced, which caused a similar message to appear. See also. Retrieved 2010-09-23.
28 January 2005. Retrieved 8 June 2014. An 18-month prison sentence is probably the best that Jeffrey Parson could have realistically hoped for. Authorities have demonstrated their determination to deal with virus writers and other cybercriminals,' said Graham Cluley, senior technology consultant for security software company Sophos. Iain Thomson. Retrieved 2010-09-23.
Retrieved 2010-09-23. Retrieved 2010-09-23. Internet Security Systems, Inc. Retrieved June 8, 2014. December 9, 2003. External link in publisher=. Malware encyclopedia.
Microsoft Corporation. Retrieved 2014-06-10. Retrieved 9 June 2014.
Retrieved 9 June 2014. Forum article on 'able2know'. Retrieved 9 June 2014. External link in title=. ^. July 25, 2003. Retrieved 9 June 2014.
Retrieved 9 June 2014. Retrieved 10 June 2014. Retrieved 9 June 2014. Retrieved 9 June 2014. Retrieved 10 June 2014. Retrieved 2010-09-23.
Retrieved 2011-03-25. HP Customer Care. Retrieved 14 February 2013.
SpyHunter is a powerful, highly effective malware remediation tool designed to assist the average computer user in detecting and removing malicious threats from their PC. As malware continues to evolve and become more sophisticated to avoid detection by anti-spyware/anti-virus programs, SpyHunter responds with advanced technology to stay one step ahead of today’s malware threats. SpyHunter offers additional customization capabilities to ensure every user is able to custom tailor SpyHunter to fit their specific needs. SpyHunter has the ability to detect and remove rootkits, which are used to stealth install ransomware, rogue anti-spyware programs, trojans and other security threats. Rootkits use hidden and encrypted files and folders to avoid detection by traditional security software. SpyHunter’s newly integrated advanced rootkit detection technology allows it to perform an instant rootkit scan and promptly display a message upon detection.
SpyHunter will then ask the user to reboot the computer and will remove the rootkit during the reboot process. In order to remove rootkits completely, Windows must be stopped upon boot because rootkits utilize other files that load and run with Windows.
Therefore, to prevent rootkits from regenerating on a user’s computer, we’ve incorporated a customized OS into SpyHunter that allows your system to be booted without Windows so that the rootkit may be removed from your computer. If SpyHunter is not able to automatically remove a malware object, the Spyware HelpDesk, an interactive feature integrated into SpyHunter, allows our technicians to remotely analyze your machine and directly deliver a custom fix to specific malware problems that may be unique to your computer.
SpyHunter Scanner SpyHunter has been carefully engineered to be powerful and complete enough for the most demanding technical professional, yet simple enough for a first-time computer user to utilize safely and effectively. With just a simple click, SpyHunter Scanner will scan your computer’s memory, registry, cookies, and files. Items found to be infected will then be listed for you. To find out more information about a specific object, merely select it.
When you are ready to remove any detected items., all you have to do is check the box next to the item and hit the 'Next' button. All objects that you remove are then placed in SpyHunter’s quarantine area. Simple as that! Spyware HelpDesk New to SpyHunter, is the Spyware HelpDesk, a unique and highly effective interface through which you can contact our support department 24/7 to solve any malware-related issues.
Firefox Patch Virus
The Spyware HelpDesk consists of two separate sub-systems: the SpyHunter Support Ticket System, and the Custom Fix System. If you experience any issues with SpyHunter whatsoever, or have any questions, comments or suggestions related to SpyHunter, we strongly encourage you to utilize the SpyHunter Support Ticket System. If SpyHunter is unable to remove an infection from your computer, our technical support department will be happy to generate a customized fix for you, which through SpyHunter you can execute to eradicate any infections lurking on your system. Please note, however, that these services are only available with the paid, full version of SpyHunter.
Network Sentry SpyHunter’s Network Sentry is included within the Settings panel area. The Network Sentry is designed to give you complete control over your system networking settings, and to prevent malicious objects from modifying and disrupting your Internet connection. In addition to HOSTS file protection, SpyHunter also offers an option to protect other Windows system files from unauthorized modifications. SpyHunter also contains advanced functionality designed to prevent malware from hijacking your desired Internet Explorer homepage. Lastly, SpyHunter has the ability to monitor your DNS servers and notify you if an unsolicited modification takes place.
This prevents tricky Trojan and malware organizations from redirecting you to a phishing or malware site. Scan Scheduler SpyHunter’s Scan Scheduler can be setup and easily configured through the Scan Scheduler area under the Settings panel. The advanced Scan Scheduler feature allows you to run a complete SpyHunter scan at a pre-set time, even if you are away from your computer. Easy to access and use, the Scan Scheduler allows you to pre-set the scan time at daily, weekly and monthly intervals. If you opt for the daily scan, you can choose to run the scan every day, every other day, every weekday, or at any interval of days that you choose. If you choose the weekly scan, you will be able to select the day of the week that your scan will be scheduled for, and for the monthly scan, select the day of the month that your scan will be scheduled for.
Please note that your computer must be powered on at the time that your scan is scheduled to run. If the computer is not turned on, the scan cannot execute! Custom Scan SpyHunter includes a new feature called Custom Scan. Custom Scan allows you to save time by limiting your scan to specific sections of your computer. With SpyHunter's Custom Scan, you will be able to select the following scan types: Memory, Registry, Cookies, Files or Rootkits.
W32 Blaster Removal Vista
A Custom Scan may only take a fraction of the time that a Full Scan would require. Even though a Custom Scan may not catch some residuals, it is an excellent choice for occasional system scans when you are trying to save time. Exclusions New to SpyHunter is an Exclusions Panel. The Exclusions feature in SpyHunter allows you to select objects that you wish to exclude from detection in future SpyHunter system scans. In some cases, SpyHunter may detect programs that you do not desire to remove.
In this case, the exclusions panel will allow you to exclude individual programs from being identified. Once selected, the programs selected in the exclusions list will not be included or detected in any future scan processes. When you are ready to add an item to the Exclusions list, it is very easy to do, simply right-click on a detected item in the SpyHunter Scanner results and select “Add to Exclusions”. Removal of an item in the exclusions list is just as easy, simply select the checkbox next to the item that you wish to remove and then click the “Remove” button. General Settings SpyHunter’s new Settings panel was designed with you in mind. The General Settings panel offers several ways to customize the operation of SpyHunter for a more personalized experience, as well as giving you activation instructions in order to register for the full version of SpyHunter. Along with this, the following General Settings can be modified through the Options panel: Automatically check for updates – SpyHunter will automatically contact the Enigma Software Group servers to check for the availability of new program and definitions updates each time it starts.
Automatically download and install definition updates – SpyHunter will automatically download and install any available definition file updates. Start SpyHunter Security Suite on Boot – SpyHunter will be configured to load automatically each time you boot your computer. Start SpyHunter Scan on Boot – SpyHunter will automatically start and begin scanning your machine each time you boot your computer. Minimize Security Suite on startup – SpyHunter will start minimized, visible only as a taskbar icon.
SpyHunter’s real-time protection features will still operate at full capacity. Prompt if any important windows components are disabled – SpyHunter will monitor your Windows settings and prompt you if a process attempts to disable the task manager or other important Windows components. Prompt if web content is used on desktop – SpyHunter will monitor Windows settings and prompt you if active web content is being used on your desktop.